Your AI applications deserve more.
Find the vulnerabilities in AI apps that scanners and humans miss.
AI-enabled applications, from autonomous agents to internal copilots, are now part of the external attack surface, yet traditional pentesting hasn’t caught up.
AI Red Teaming for LLM Applications, a new Novee feature, autonomously simulates real-world attacks like prompt injection and data exfiltration. Our AI agents chain techniques and adapt in real-time, mirroring human attackers. AI-driven organizations move faster than quarterly audits; they need offensive security with the speed to match.
Start a pentest
AI-enabled applications, from autonomous agents to internal copilots, are now part of the external attack surface, yet traditional pentesting hasn’t caught up.
AI Red Teaming for LLM Applications, a new Novee feature, autonomously simulates real-world attacks like prompt injection and data exfiltration. Our AI agents chain techniques and adapt in real-time, mirroring human attackers. AI-driven organizations move faster than quarterly audits; they need offensive security with the speed to match.
Chosen by teams that take attackers seriously
Novee is different

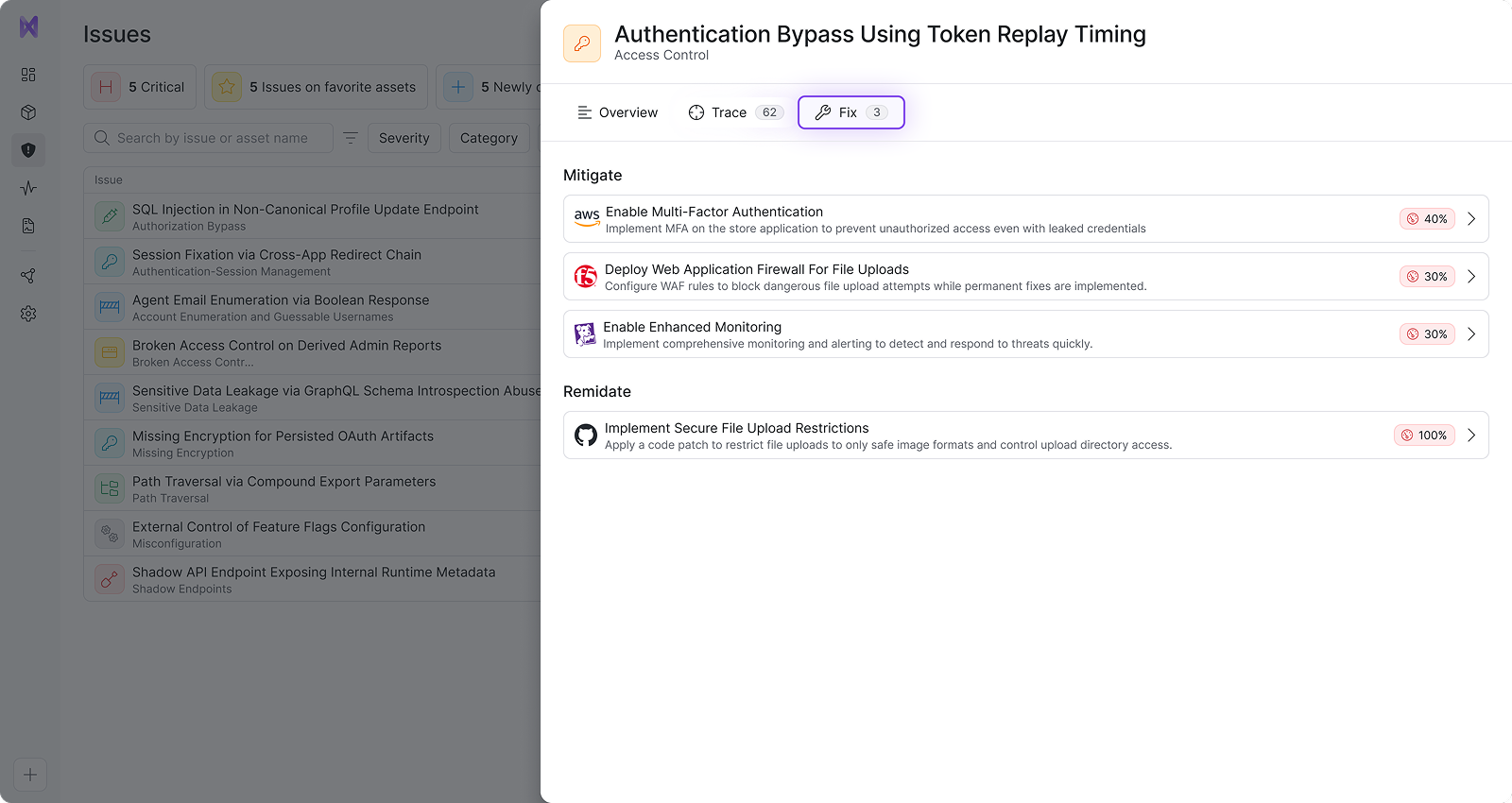
AI that delivers personalized fixes
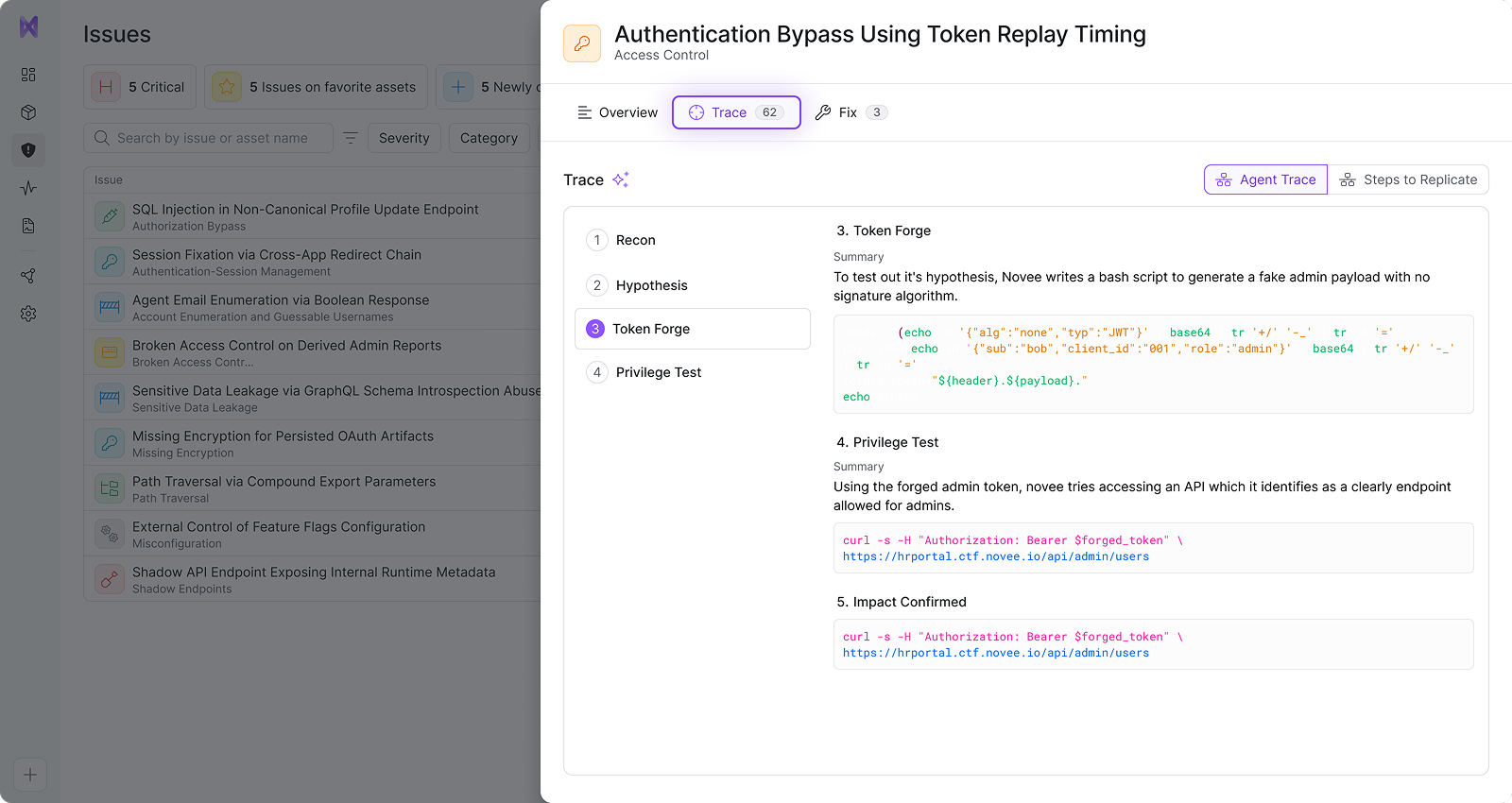
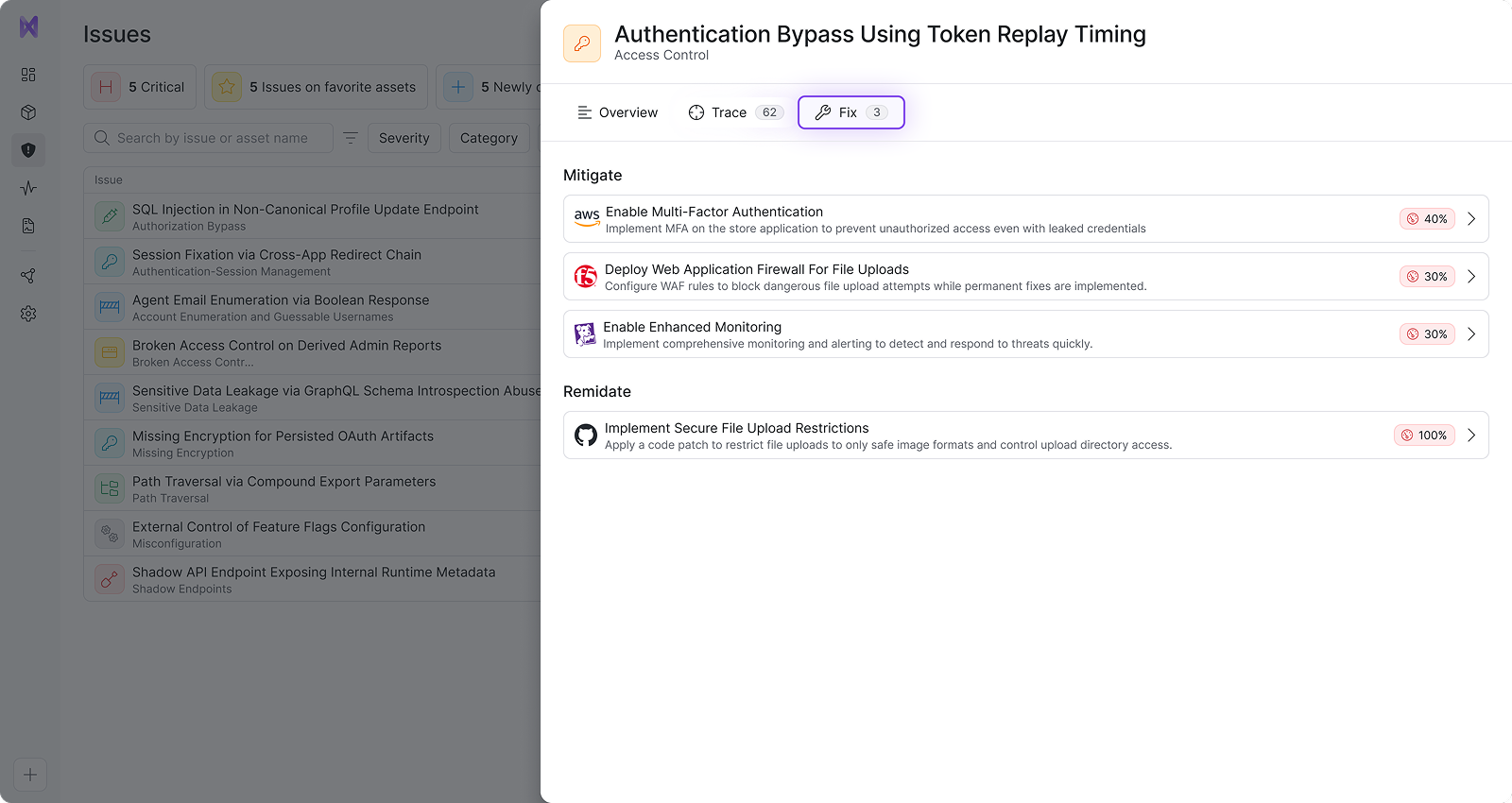
Manual penetration testing and scanners stop at detection. Novee discovers, validates, and tells you exactly how to fix each issue – then automatically retests to verify the fix.

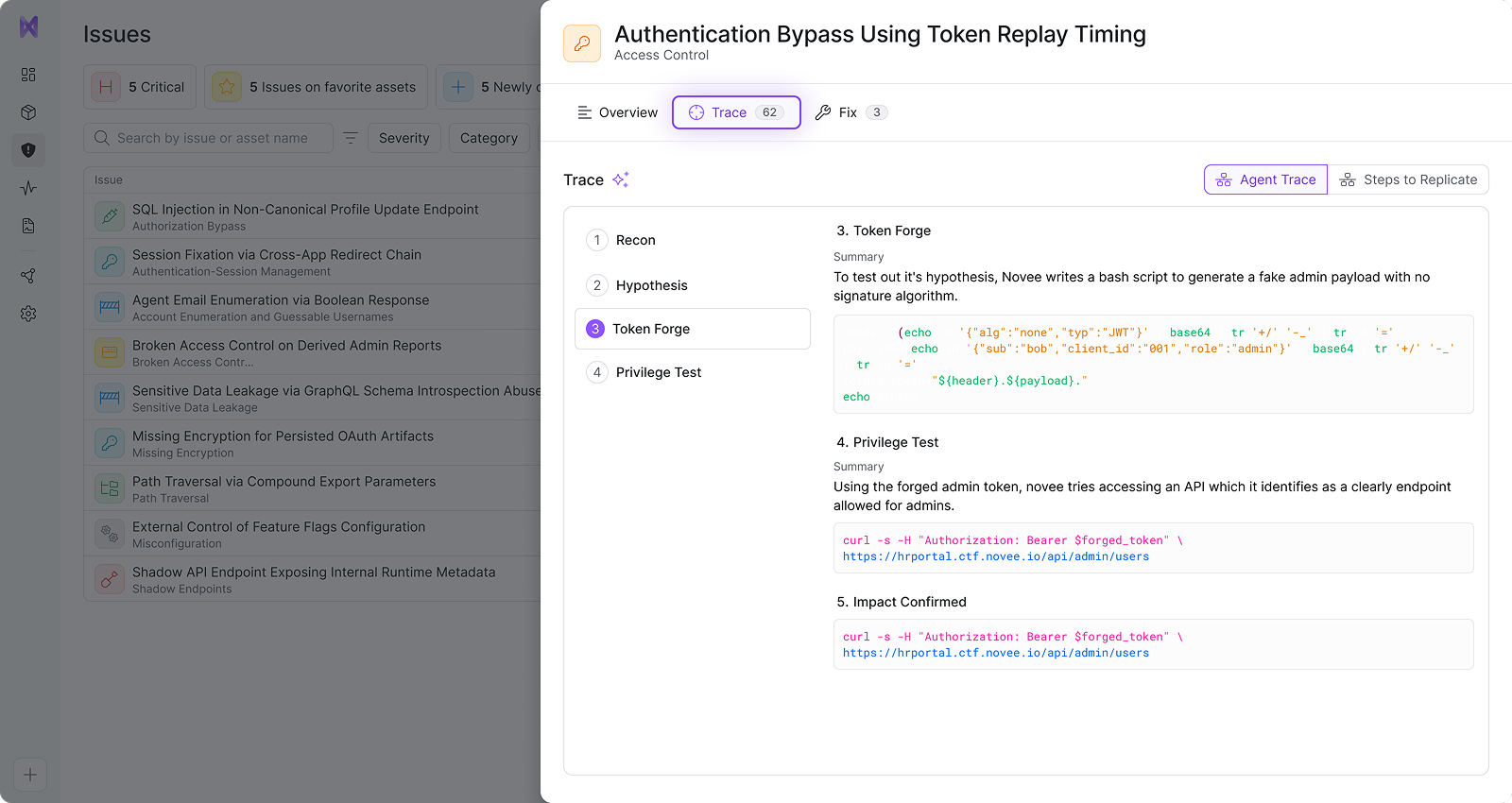
Attacker-trained AI reasoning model
We distill offensive tradecraft, tools, and exploitation knowledge into a specialized reasoning model that outperforms general LLMs on cyber-specific tasks – so findings reflect real attack behavior.
AI attacker that can start black box
We can begin like a real adversary, with zero knowledge – and then expand into gray- and white-box context for deeper coverage. (So you get value immediately without exposing crown jewel access.)
Attackers have an unfair advantage

Your environment’s changing fast
AI coding assistants and vibe coding help you push new code faster than you can secure it – leaving giant blind spots for attackers to exploit.

AI has made the job so easy
Launching advanced persistent attacks used to take time and skill. Now it’s automated, continuous, and running 24/7.

Traditional security testing is theater
A once-a-year pentest? Perfect. That’s 364 days to run wild – especially when automated scanners only catch generic, known vulnerabilities.
AI penetration testing that keeps you one step ahead of attackers
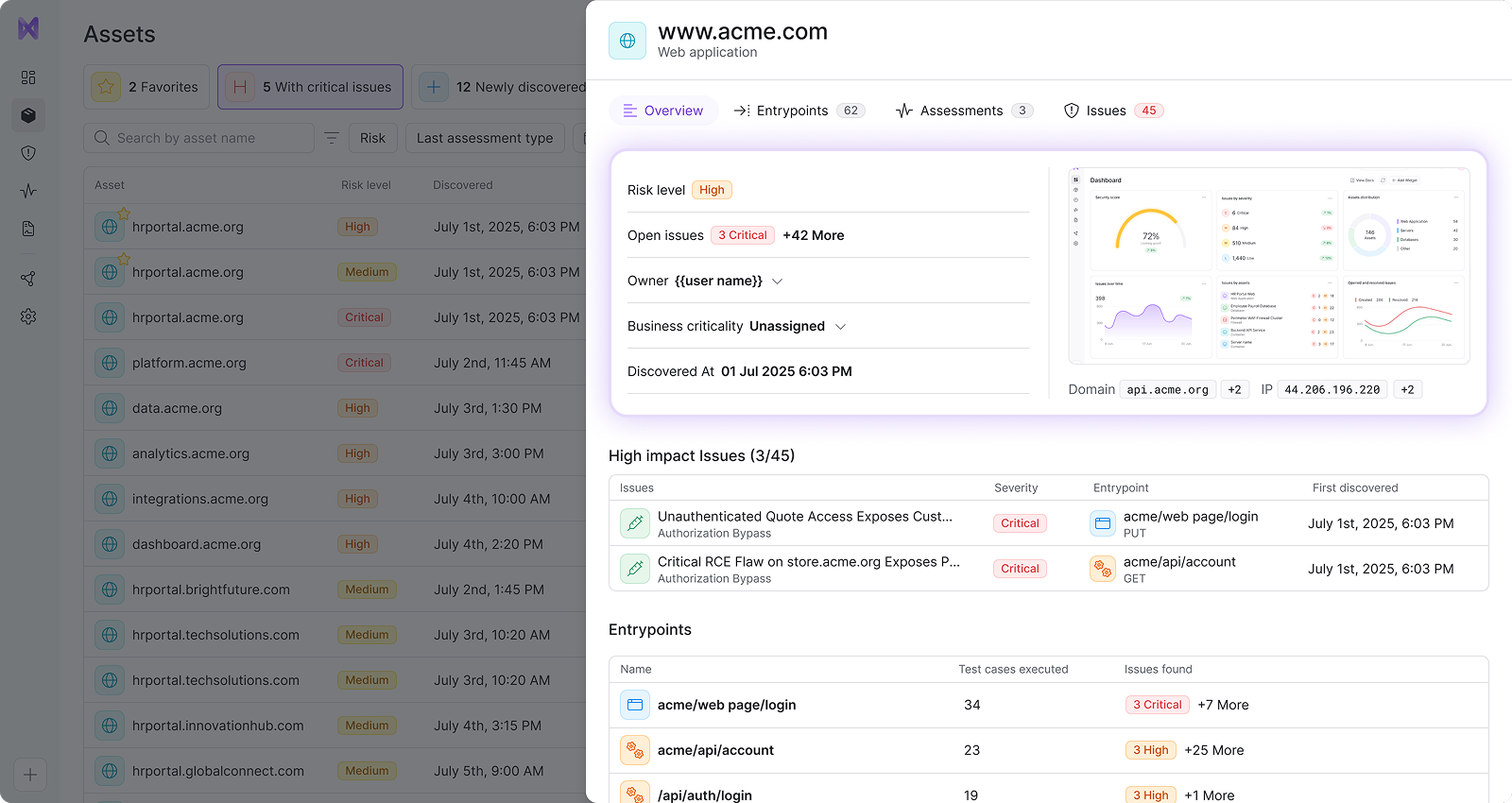
Discover
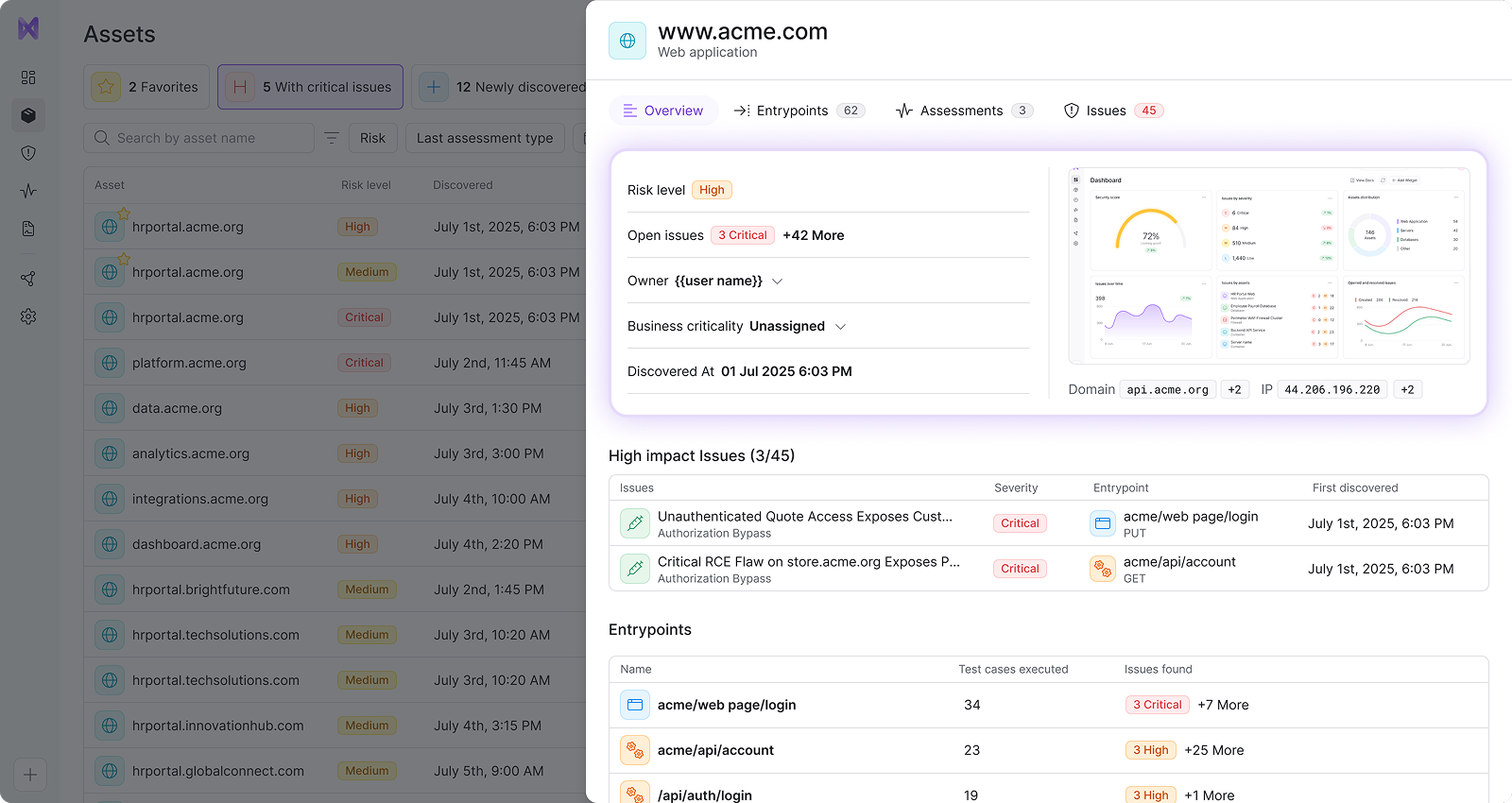
See what your attackers see
Continuously map your live environment the way an attacker would – by interacting with real flows, endpoints, and behavior to understand what’s actually exposed.
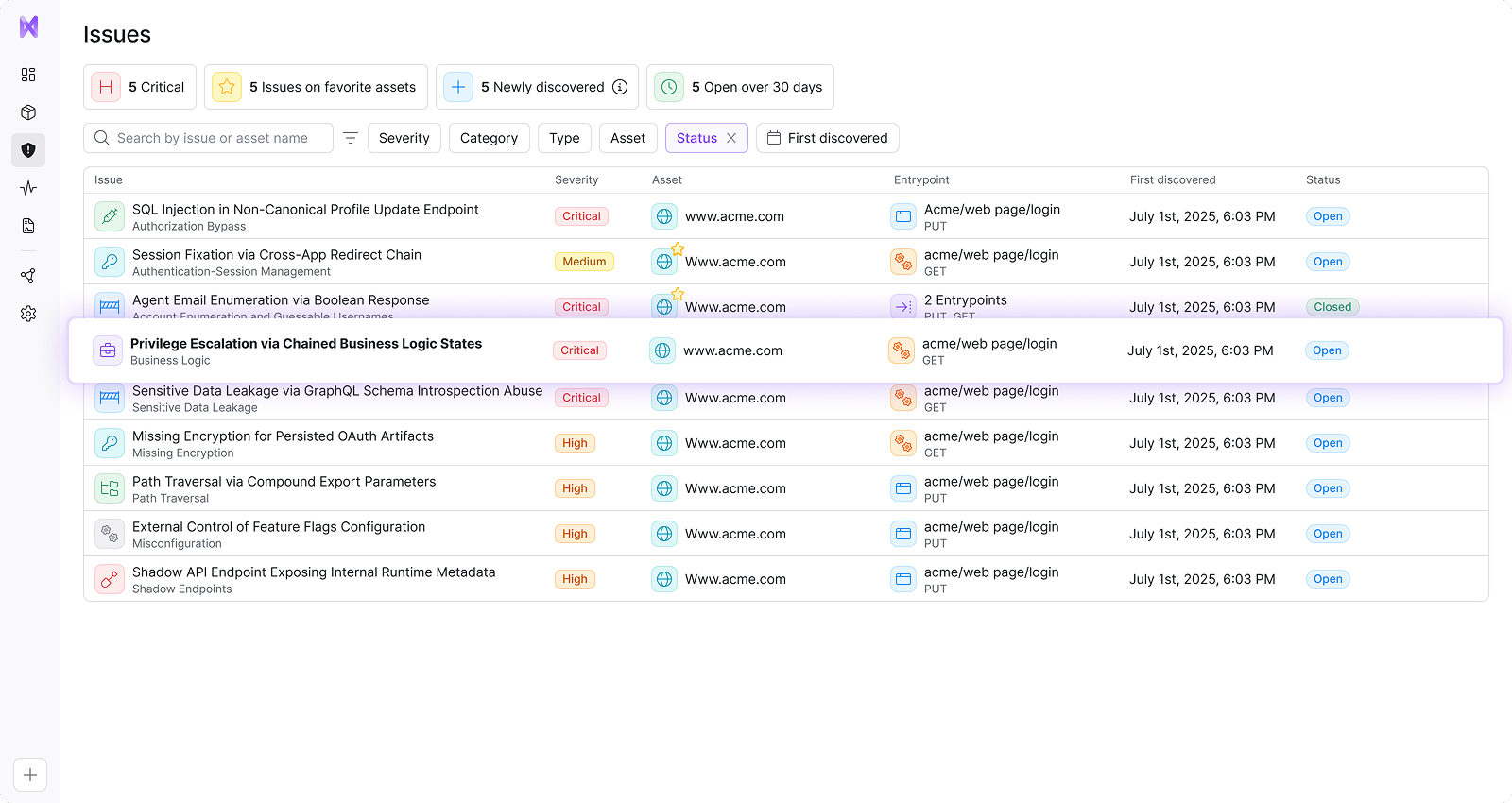
Detect
Find weaknesses before hackers do
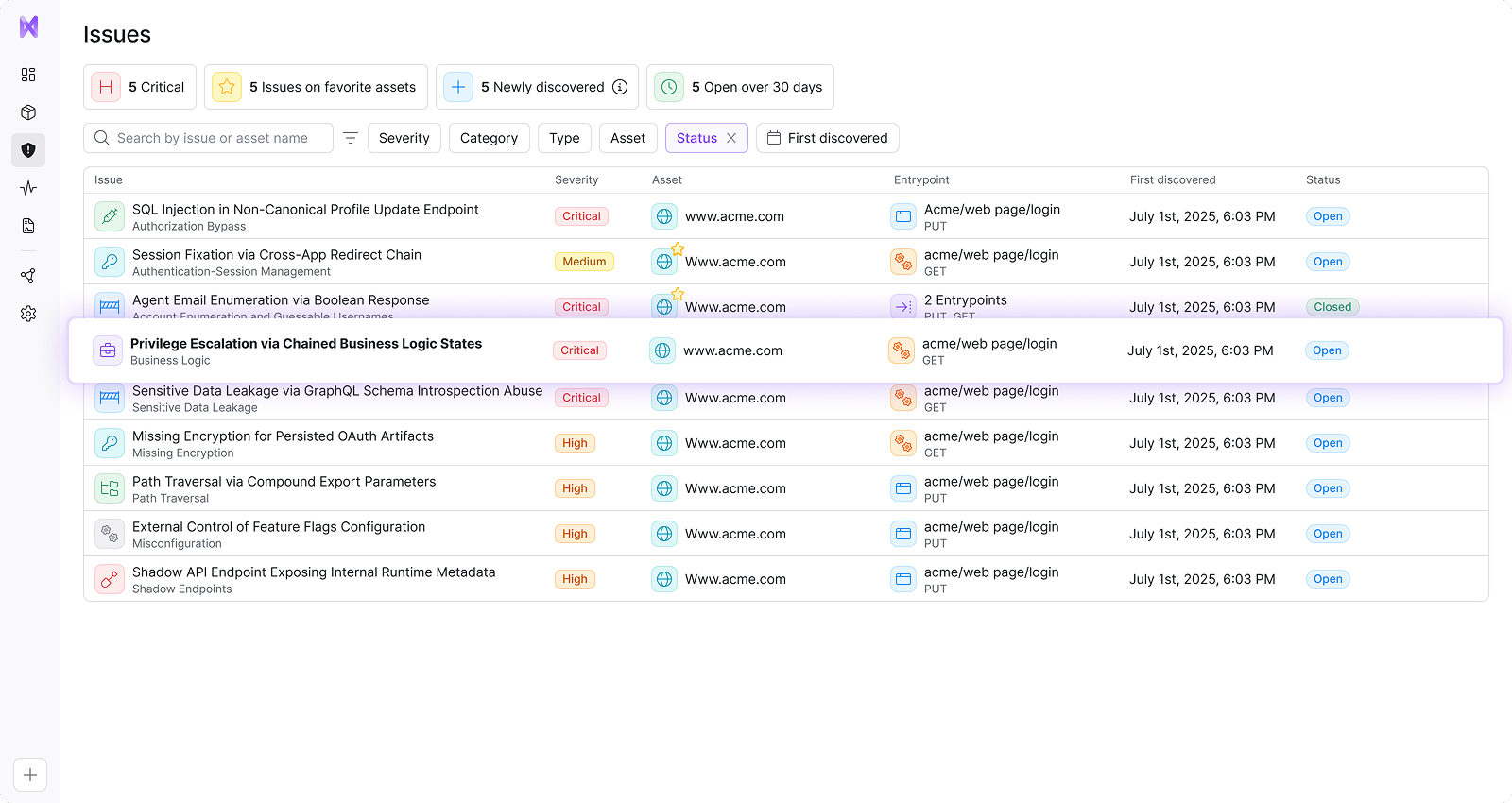
Continuously attack your applications to uncover real exploit chains, business logic flaws, and vulnerabilities that scanners consistently miss.
Validate
Focus on real issues, not false positives
Every issue is confirmed with clear steps to replicate and real impact, so your team can ignore false alarms and focus only on issues that truly put you at risk.
Fix
Remediation that fits your exact environment
Get clear, personalized, step-by-step fixes tailored to your architecture, tech stack, and business logic. (Not generic scanner advice.)
Repeat
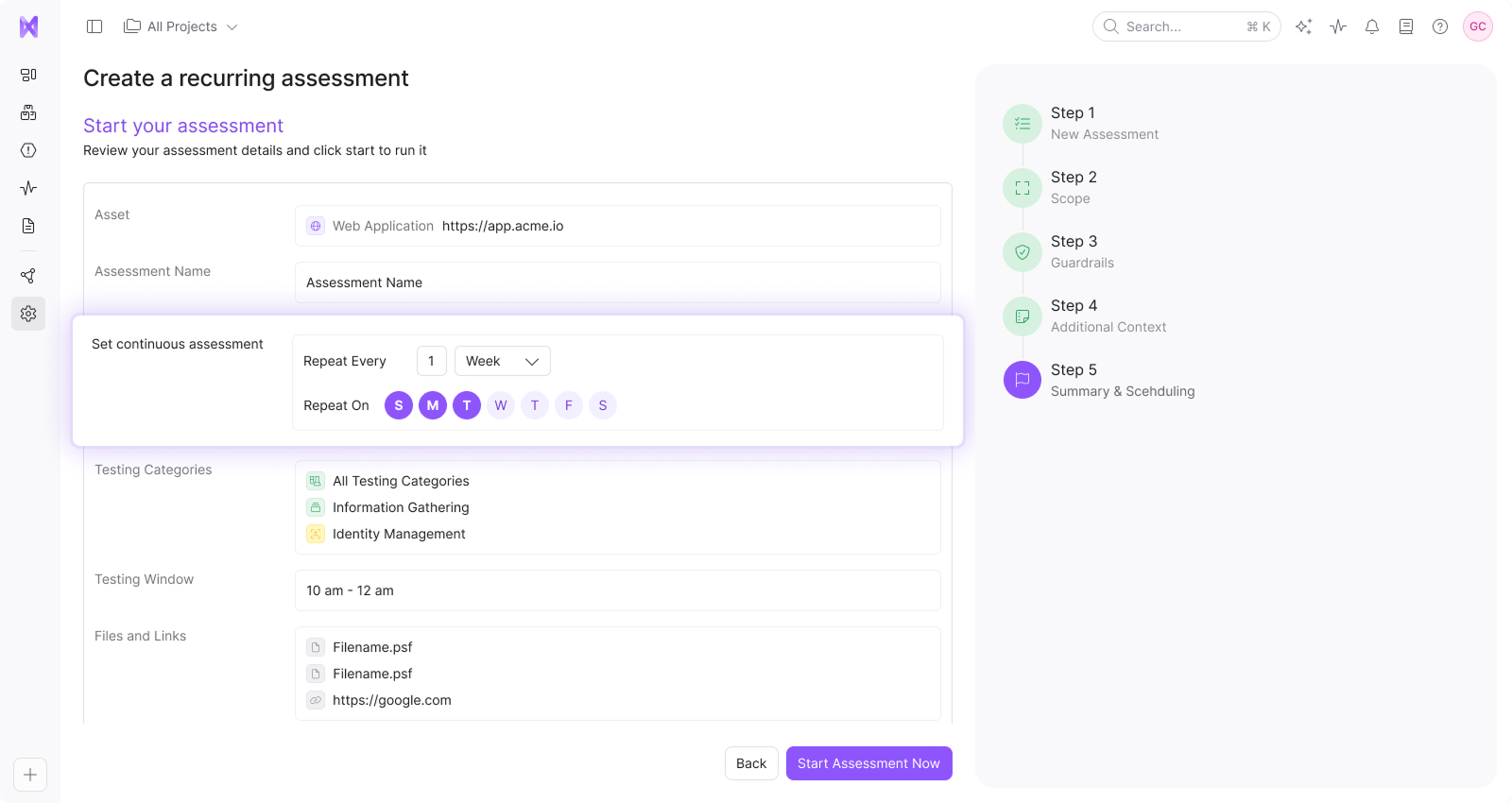
Protection that adapts with you
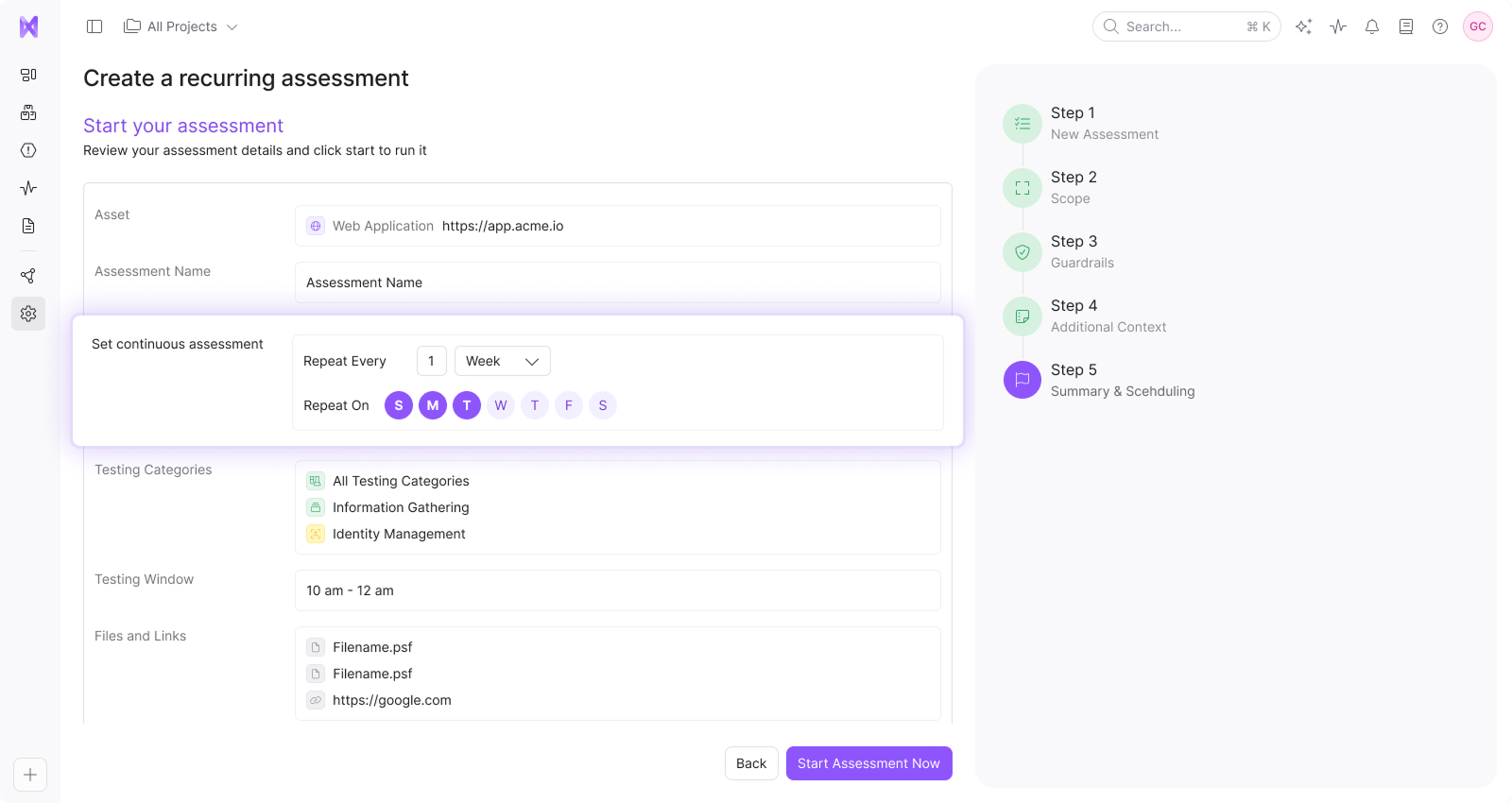
Automated assessments adapt to your evolving infrastructure – retesting with new deployments, code changes, and emerging threats.
What security leaders say
Inside Novee's
AI hacker
We built an AI hacker that thinks like the attackers we used to be, and armed it with years of offensive security knowledge and techniques.






